Protecting Implantable Medical Devices From Malware, Side-Channel Attacks
By Jof Enriquez,
Follow me on Twitter @jofenriq
University of Arizona researchers are trying to shore up implantable medical devices' defenses against cybersecurity threats by developing technologies to better detect malware and thwart side-channel attacks.
Many implantable medical devices, like pacemakers and defibrillators, have the ability to transmit clinical data remotely to allow providers to assess the patient's condition and tweak technical settings. But hackers also can gain access to confidential patient data, and could use malware to harm patients, as “ransomware” or to “medjack” these devices to infect other interconnected devices or IT systems.
A safety communication notice issued by FDA in January has highlighted the inherent vulnerability of cardiac implants, which are implanted in hundreds of thousands of people in the United States.
Engineers at the University of Arizona are trying to fix these vulnerabilities from every angle, including assessing how implants transmit data safely, optimize power consumption, and handle electromagnetic radiation.
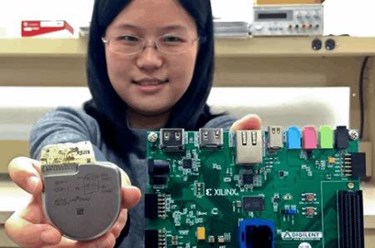
Roman Lysecky, a recipient of a prestigious National Science Foundation Early Career Award and an associate professor in the UA's Electrical and Computer Engineering Department, has built a prototype of a network-connected pacemaker, and is running experiments on how to detect malware and keep infected devices from malfunctioning.
In an NSF-sponsored study, Lysecky and co-principal investigator Jerzy Rozenblit — UA Distinguished Professor, Oglethorpe Endowed Chair in the Department of Electrical and Computer Engineering, and a professor of surgery in the College of Medicine — are developing runtime anomaly detection technology to reveal suspicious changes in the timing of how the device computes and transmit data from a pacemaker to a cardiac log. Deviations from the device's normal, precisely-timed processes could indicate the presence of malware. If changes are detected, doctors are informed promptly so they can take corrective action to prevent harm to the patient.
Lysecky and colleagues are also using runtime anomaly detection in their prototype pacemaker system to look for malware mimicry, whereby hackers tweak malware to resemble normal device characteristics and functioning to avoid detection.
In another project supported by a grant from the Army Research Office, Lysecky and co-principal investigator Janet Meiling Roveda, a UA professor of electrical and computer engineering, are developing mathematical models to analyze changes not only in timing, but also in power consumption and electromagnetic radiation.
“Side-channel attacks like these are a critical threat to the security of embedded systems,” Lysecky said. “By analyzing data transmission timing, power consumption and electromagnetic radiation from a life-critical device such as a pacemaker, a hacker can extract data like cryptographic keys that are essential for shielding communications from unauthorized users.”
FDA is putting more emphasis on cybersecurity, and is encouraging device manufacturers to implement cybersecurity measures during their products' total life cycle.
“We believe manufacturers should build implantable medical devices like pacemakers with malware detection strategies from the get-go, and provide patches as future problems develop,” said Lysecky, in a news release.
The agency also has issued premarket and postmarket cybersecurity guidance documents. So far, there have been no reports of loss of life or harm to patients directly attributed to hacked devices. The growing prevalence of connected medical devices, though, has experts worried.
“It used to be we only had to worry about breaches of our computers and smartphones,” said Lysecky. “Industry analysts predict that by 2020 most of the 20 billion electronic devices on the market will be interconnected – and millions of these will be implantable medical devices.”
